Given the tight labor market for cyber security talent, how is your company addressing cyber exposure? To help narrow the skills gap, companies are incorporating knowledge sharing, crowdsourcing research and using automated tools to scale up their operations. We list 7 ways you can apply these three options to scale up cyber capability.
1. Increase adoption of security tools by integrating with existing tools.
One way to increase security awareness is to integrate security into existing workplace tools. For example, an integration with Slack enables employees to start to see security and vulnerability scanning as part of their workflow.
2. Make security training compulsory and fun with a variety of on-demand media.
To scale up cyber security, people who are not part of the security team also need to think and care about it. This was a key takeaway for scalable cyber security from both the AppSec EU and Black Hat security conferences and is commonly discussed in the infosec community.
Compulsory educational training for all employees - particularly for developers - is one way to do this. Knowledge-sharing can be delivered in different formats to increase adoption and learning. The information can be set up as a separate knowledge platform (e.g., a wiki or internal library) with instructional videos, knowledge quizzes, internal knowledge sharing blogs, suggested external links. The message is that security is everyone’s responsibility, and everyone should be aware and vigilant. Below is an example of an educational video from Detectify.
3. Foster security champions in the development team to spread the gospel.
Few growth-stage companies have a security team; if they do it’s typically only one or two people working with all types of security from network to application. Since developers vastly outnumber security professionals, the opportunity exists in development teams to build up security champions on specific security topics and encourage a proactive security mindset earlier in the development cycle. Not every CISO or Security Engineer has time to explain common terms (e.g., XSS) to every single person each time the question comes up.
This is why having topic owners on teams goes a long way to having security as part of the development culture. In additional to general security posture training for all employees, an internal security wiki for developers should exist with key terms, lessons learned and a repository of best practices. This includes samples showing code remediation tips in order to avoid exposing vulnerabilities in the application.
4. Invest in proactive security knowledge for developers.
The key to scaling up security practices is educating developers as they code and build product. Security needs to be something they think about starting with design and from the first line of code. Products like Checkmarx enable developers to deploy static code analysis for known vulnerabilities during the build process, while Detectify scans dynamically to check for vulnerabilities during staging and production. With the immediate feedback, developers can fix the code before pushing it live.
5. Gamify knowledge by running CTF competitions.
Capture-the-Flag (CTF) events are ways to gamify information security education. This kind of activity requires participants to complete different trivia and coding challenges. There are two main styles - Jeopardy and Attack-Defend. The first requires participants to answer different questions to gain points and advancer further in the competition. The second has participants on an attacking team or defending team – defenders try to protect and patch their vulnerable application from the attackers.
Both sides have to utilize their coding skills to keep each other out. Both CTF competition styles help security interested programmers develop skills in an interactive way. For coders, Checkmarx has a codebashing educational platform for identifying vulnerabilities. Most developers identify codebashing with fixing bugs, but Checkmarx’s product helps educate developers on coding security defects.
6. Crowdsourcing: the more eyes on your security the better.
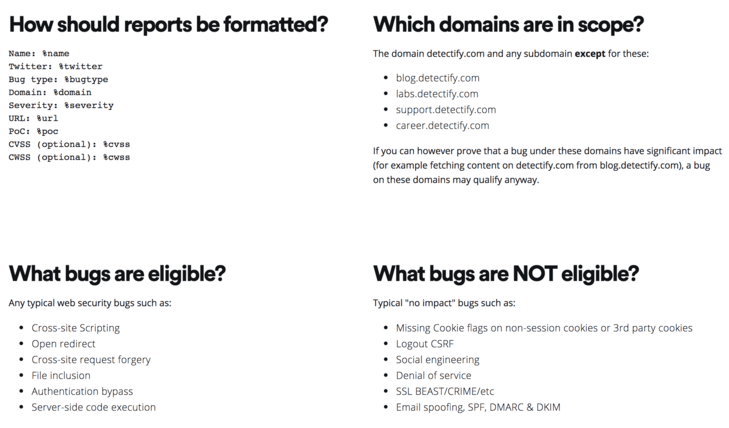
Cybersecurity crowdsourcing involves using external, security savvy, developers/ testers (white hat hackers) to find vulnerabilities in the code base. Companies invite ethical hackers to legally hack their web applications to find vulnerabilities faster. To establish such a program, companies set up a Responsible Disclosure policy or bug bounty program.
The benefit of crowdsourcing is threefold. It scales up security operations through using broad resources. The second is speed since vulnerabilities are identified and remediated quickly. It also improves vulnerability detection because ethical hackers provide diverse skills from the forefront of security. Ethical hackers reveal their break-in methods and what needs to be fixed, while internal developers and security teams focus on expediting the patches, learning about the new vulnerabilities and optimizing their security practices using the crowdsourced feedback. Code oriented security audits often only occur once a year and with crowdsourced security, they can happen more frequently.
7. Automate the tedious security tasks.
If it can be automated then it should be automated applies to most all aspects of testing, building and releasing software. This also applies to cyber security. Automated tools exist to help relieve programmers and QA resources from having to manually check thousands of lines of code for vulnerabilities in the web application. The goal is to use tooling to automate tasks so that human resources can focus on core competencies and things that automation is not good at confidently detecting.
Automation on its own will not replace all security testing tools, but it can be added to complement human skills in manual vulnerability testing or maximize the value of bug bounty programs and scale up cyber security.
Closing comments
Scalable cyber security begins with small shifts in how a company manages the flow of security education. Knowledge is power, which is why it’s critical to educate people and build up security champions to spread security awareness throughout the organization. Even as cyber security talent is in short supply innovative approaches like crowdsourced security and smarter automation tools can solve this problem and help companies shift to a security-focused mindset.
About Detectify
Detectify was born from the simple idea that the internet was broken. The team of founders are some of the best ethical hackers in the world who’ve hacked tech giants like Google, Facebook and Dropbox. Today we offer a web application security scanner that automates hacker attacks to detect 1000+ known vulnerabilities including OWASP Top 10, DMARC-records and misconfigurations in CORS and Amazon S3 buckets. We are trusted by some of the most widely used consumer products such as Spotify, Trello and King. Based in central Stockholm, Sweden, we are currently a team of 40 employees and growing quickly. www.detectify.com
Given our awareness of security challenges, it’s not surprising that Insight has invested in several security companies making a difference in protecting network, application, and infrastructure security. To see some of the best-in-class solutions, take a look at the ways in which, Checkmarx, Cylance, Darktrace, Detectify, FireMon, Prevalent, Recorded Future, Mimecast, SonarSource, Sift Science, Tractable, Resolve Systems and Tenable can help you.