Identity and Access Management (IAM) in the age of AI Agents
The trend to adopt AI Agents within enterprises is expected to continue to accelerate. BNY, as an example, has already deployed 130 ‘digital workers’ with human managers, and other large enterprises are seeing transformative success in areas like software development and customer success. Palo Alto Networks’ CEO Nikesh Arora recently commented on their latest earnings call that we are “entering the next phase of AI adoption,” as “large enterprises are moving beyond experimentation and beginning to integrate foundational models into real workflows.”
Recent threat reports from both CrowdStrike and Palo Alto Networks Unit 42 are a powerful reminder that identity has become the primary attack surface, with CrowdStrike observing that “82% of detections” are “malware-free.” Intrusions moved through authorized pathways and trusted systems, blending into normal activity. Palo Alto Networks has noted that compromised identity has become attackers’ most dependable route to success, proving significant in nearly nine out of ten Unit 42 investigations.
This is a stark warning for enterprises deploying AI Agents. Identity is already a complex topic, and the acceleration of these ‘digital workers’ will likely lead to increased opportunities for threat actors to exploit poorly managed Agent credentials and over-privileged Agent identities. This calls for an uplift in processes and innovative technologies to help stay on top of an otherwise rapidly escalating risk.
Last year, we wrote about the need for enterprises to rapidly define how they intend to secure AI Agents in their environments. We see continued innovation here as the real-world deployment models for AI Agents in the enterprise begin to take shape — and we have provided an extensive, updated perspective as the final section of this article. We have further developed a framework for how enterprises can consider deploying an increasingly mature set of technological capabilities for securing AI Agent deployments.
There is a potential existential risk for companies that do not adopt agentic capabilities fast enough; however, in order to do that safely, Agent Identity and Access Management (Agent IAM) needs to be solved, making it the defining security topic for 2026. This article dives deeper into the topic of Agent IAM, and where we see the need for innovation to cover the gaps in current technology and enterprise deployments.
Enterprises are starting with Agent identity, but that’s not the biggest challenge
As we continue to talk to enterprises about the challenges associated with Agent identity, one thing is clear: Most Enterprises want to treat AI Agents as digital employees — provisioning them with unique, global user identities the same as any human employee would have, and assigning them an owner or manager.
This is an elegant solution for identity, but doesn’t really solve many of the problems associated with Agent IAM; the ‘I’ is for identity, but what about access management?
The diagram below sets out a basic architecture and credentials flow for deploying AI Agents in this manner.
Already, we can highlight a few challenges that extend beyond managing traditional human identities:
- Permissions and entitlements are hard to manage, even statically. Agents will likely need dynamic permissions (where robotic process automation, RPA, was predictable), and governing those permissions in real-time will present a significant challenge, whilst preventing excessive privilege creep.
- Tracking delegated permission scopes and identity origination (i.e., who or what instigated the action) through multi-hop delegation will be a challenge. Current standards (e.g., OAuth) don’t suitably account for this, leading enterprises to explore custom implementations while waiting for updated common standards (e.g., those currently in draft by IETF). This problem is exacerbated by the need for ephemeral Agents that may be spawned temporarily to complete a task and must inherit a strict permissions set from their parent Agent or process.
- Agents need a broad set of credentials, including the credential zero problem. In a world that was trying to move away from credentials management, this feels like a step back for security. Fundamentally, this is a non-human identity (NHI) challenge at scale and may require new solutions that use deep authorization decisions, zero standing privileges (ZSP), or just-in-time (JIT) access for Agents.
- Related to that, biometrics don’t exist for Agents, meaning we’re back to ‘credentials management’ at scale. Although it also presents an opportunity to embed best-practice approaches, such as the Secure Production Identity Framework for Everyone (SPIFFE/SPIRE) — which is supported by established players like Keyfactor* — consistently across enterprise environments.
- Finally, we need to look beyond just access management for Agents and toward action management. Due to the non-deterministic nature of Agents, we need to monitor how they’re leveraging the access granted to them. Just because an Agent has access to something, it does not mean it should have free rein over that access. This is the same for humans and is an extension of the insider threat problem, applied to Agents.
The 2026 concept paper by NIST is an early indication of the standards and guidelines that will become available for enterprises (and extensive documentation is available for Agents deployed in hyperscaler platforms, AWS being a good example). However, the broader development and adoption of those standards and guidelines are already lagging behind the rapid deployment of Agents we’re witnessing today, leaving enterprises with little choice but to address these challenges themselves.
Agent IAM will drive the next wave of identity capabilities
The core ‘identity’ part of the IAM challenge for Agents can likely be addressed by enterprises leveraging or extending the capabilities of vendors that exist today. However, access management, action management, and permissions (particularly with multi-hop delegation) will likely need new solutions or approaches. Additionally, the complexity and dynamic nature of the identity management challenge could also open the door for new entrants in the Identity Governance and Administration (IGA) space that are more flexible and agile for the future needs of the enterprise.
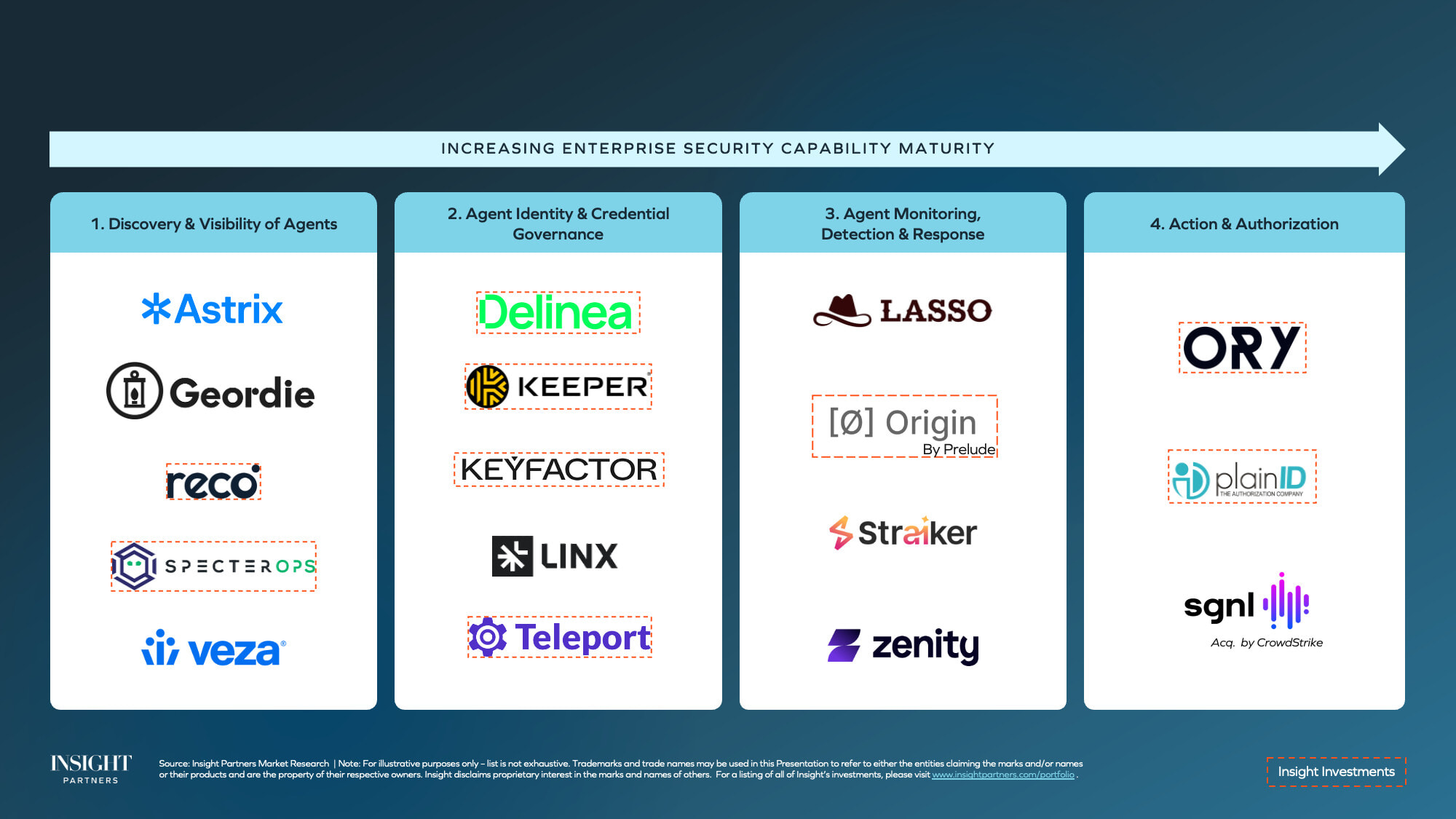
Aligned with our previous framework, the problems outlined for Agent IAM fall into three broader opportunities for innovation:
- Solving identity origination and traceability, including through the multi-hop delegation challenge.
- Intent monitoring and ‘action management.’ First, tying action to intent, and then monitoring for deviations from that. This is the User and Entity Behavior Analytics (UEBA) and Insider Threat problem for Agents.
- Solving permissions management and dynamic authorization, which can be approached with a combination of Zero Standing Privilege (ZSP), JIT access models, and dynamic authorization solutions.
As Arora pointed out in the earnings call, “We support this perspective and are excited to see new entrants in the Agent IAM and broader AI Agent Security space that have the potential to displace incumbents’ capabilities and platform vendors, who are themselves attempting to reposition as agentic security solutions.
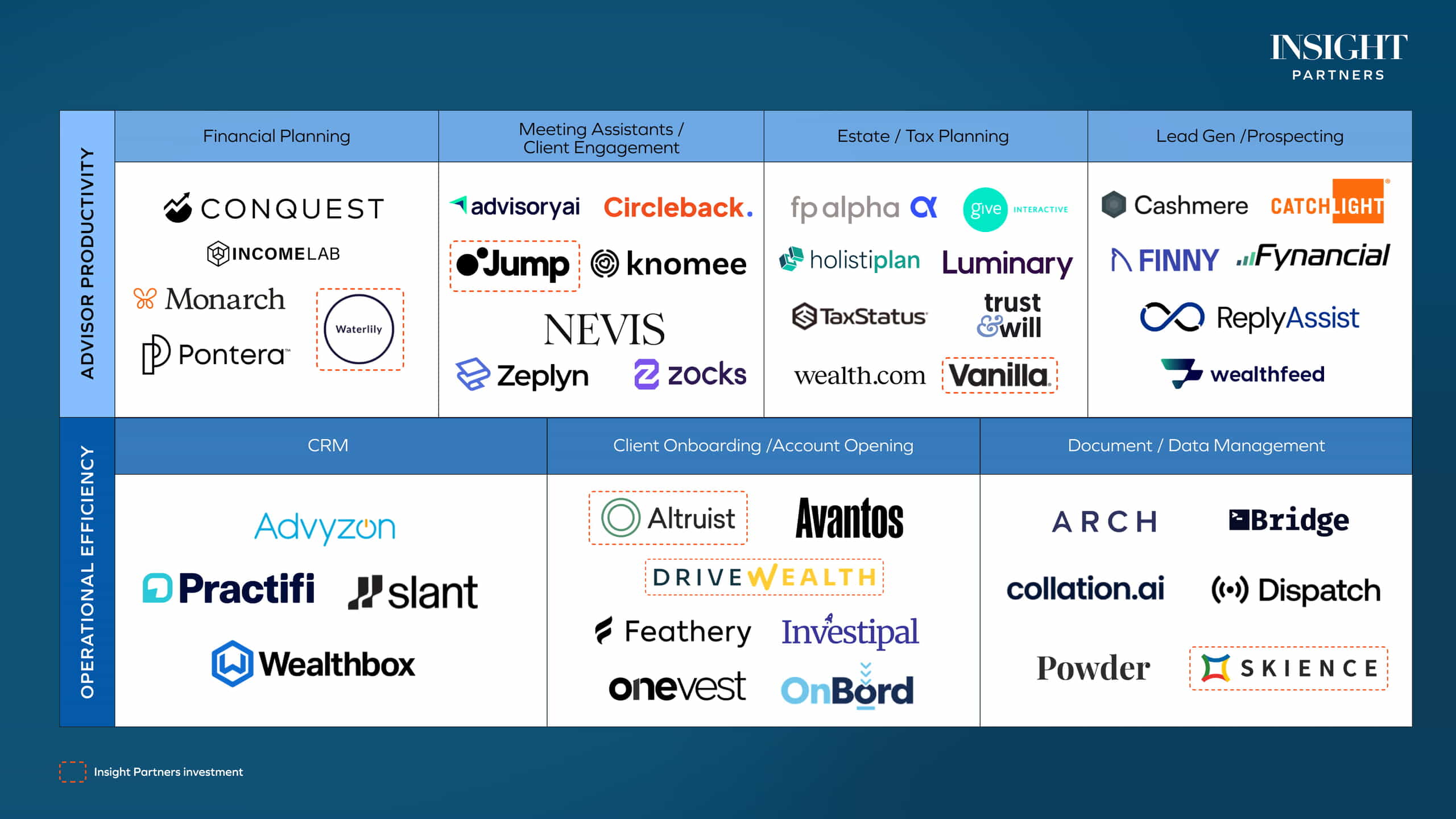
An update on the broader AI Agent Security landscape
As with previous technology transformations, securing AI Agents will require revisiting security control domains and assessing whether they are fit for purpose for how Agents (and, more broadly, Agent-driven architectures) will be deployed and operate, or where new technology capabilities are needed. We’ve seen some significant innovation since first writing about this topic in October.
As an example, ‘on-device Agents’ (or End User Agents, EUAs) are becoming increasingly prolific as a standard deployment model, initially for developer productivity but soon to be expanding to broader use cases — and open-source, consumer-focused releases like OpenClaw have begun to raise awareness of the potentially catastrophic implications these EUAs could have once deployed into enterprise environments.
Security innovation accelerates across endpoints, SaaS, and cloud
We’re already seeing promising innovation in solutions like NanoClaw and OHaaS: more security-deliberate alternatives to the ‘off-the-shelf’ open-source OpenClaw. Prelude* has recently developed a new endpoint security product, Origin, that can monitor agentic behavior on the endpoint and can detect and respond to anomalous or malicious activity.
Established endpoint security players like CrowdStrike and SentinelOne*, with their recent acquisitions of AI model security companies (just two of many over the past 12 months that we see as the first wave of ‘AI model security’ focused acquisitions), are driving further into this space with comprehensive AI protection solutions.
Beyond endpoints, Agents are proliferating in SaaS, driving momentum for companies like Reco* that are well-positioned to help enterprises gain control of ‘AI sprawl’ across SaaS applications and embedded Agents. Similarly, cloud-native security platforms, including Tigera*, Wiz*, Aqua*, and Sysdig*, as well as established players like Palo Alto Networks and Zscaler, are already addressing agent-specific risks in cloud environments — from identity and credentialing to authentication and observability.
Agent identity becomes the new control plane
We’ve also seen the NHI space rapidly evolve, with existing players expanding to cover Agent discovery and subsequently expanding to Agent access control (with solutions like Astrix and Oasis being ‘first movers’ in this regard). And we believe consistent coverage across NHIs, human and Agent identities will be table stakes for any future IAM tool — and this is exactly how innovative companies like Keeper* and Keyfactor* are approaching the challenge.
Unifying identity across humans, machines, and Agents
Teleport*, as another example from our portfolio, provides a unified identity layer for humans, machines, software, and Agents — treating every identity as a ‘first-class citizen.’ Their solution enables consistent identity governance and secure access to AI infrastructure services, including model context protocol (MCP).
As the number of NHIs continues to accelerate ahead of (in some cases shrinking) human identities, the number of credentials or secrets associated with those NHIs also increases exponentially. One Agent may have multiple credentials associated with it. As users leverage these tools to create more software, faster, the need for solutions that can detect and help enterprises effectively remediate ungoverned Agent identities and secrets related to Agents and broadly, applications, increases dramatically. This is a core part of the thesis behind our recent investment in GitGuardian*.
From visibility to attack path management
We believe the explosion of Agent identities is a catalyst for solutions providing identity visibility, monitoring, and remediation. Companies like Veza (recently acquired by ServiceNow) have been pioneers in this space, but we also see newer entrants like Linx providing robust capabilities straddling both Identity Security Posture Management (ISPM) and modern IGA. And solutions like SpecterOps* that provide identity attack path management capabilities leveraging graph-centric approaches are expected to become increasingly important for enterprises to stay in control of Agent identity sprawl and over-privileged Agents and sub-Agents.
Agents are also driving new interest in solutions providing ZSP, JIT access, and enhanced authorization capabilities due to the heightened need for ways to manage real-time access to resources and associated permissions. Solutions like Keto by Ory (based on Google Zanzibar) enable ‘lightning fast’ permissions and authorization for all identities, and their relationship-based access control (ReBAC) model provides a more flexible and dynamic framework for Agents, addressing the limitations of static role-based access control (RBAC).
Finally, we continue to see advancements in innovation to secure the use of MCP and broader Agent infrastructure access. We continue to see new features delivered by our existing portfolio companies, not least Tailscale*, whose MCP Gateway is already being used to secure OpenClaw deployments, and Promptfoo*, a widely used AI red teaming solution with native guardrails and MCP Proxy capabilities.
Platform consolidation signals the next phase of Agent security
As this space continues to evolve, we expect to see continued momentum in strategic acquisitions with platform players looking to bolster their Agent security capabilities. The first wave already mentioned was the acquisitions of AI model security companies, of which we saw at least nine in the past 12 months alone.
The second wave — Agent identity — is already underway, with Palo Alto Networks’ acquisition of CyberArk, ServiceNow’s acquisition of Veza, and, more recently, CrowdStrike’s acquisition of SGNL. The third wave we expect to cover monitoring, detection, and response capabilities related to Agent activity, but it’s possible these will be developed internally as extensions to the features provided by the previous AI model security acquisitions, now that domain-focused expertise has been brought in-house.
This is a fast-moving technology wave, and we’ll likely see significant change not just in security solutions but enterprise architectures. We’re always keen to hear from those driving secure adoption of AI Agents. Reach out if you want to continue the conversation with our team.
*Note: Insight Partners has invested in Keyfactor, Prelude, SentinelOne, Reco, Wiz, Aqua, Sysdig, Keeper, Teleport, SpectorOps, Ory, PlainID, GitGuardian, Tailscale, Tigera, and Promptfoo.